App Connect Enterprise Quickstart¶
Introduction¶
The instructions in this section will walk you through the steps necessary for setting up a demo environment that can be quickly shown to customers to showcase the art of the possible.
This demo in no way removes the need for following the tutorial style instructions that are documented in other sections of this guide. The instructions below will set up a pre-canned application demo environment to show to the customers.
Pre-requisites¶
Create a custom Git Organization¶
Create a new Git Organization to host the different GitOps repositories.
Note
Make sure you do not populate your GitHub organization with cloned repositories. The GitHub organization must be empty and will be populated automatically by the environment provisioning.
Instructions:
-
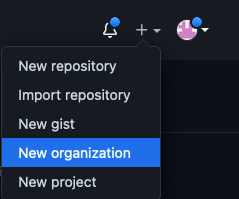
Log in to http://github.com and select the option to create a New organization.
-
Click on
Create a free organizationplan. -
Complete the wizard by filling in the
Organization account nameandContact emailfields. Select theMy personal accountbullet and complete the verification step and click Next. -
Skip the step to add members to the Organization.
-
Complete the
Welcome to GitHubquestionnaire and click Submit. -
Congratulations, you have successfully created a new Github Organization.
Note
Please ensure your GitHub organization is Public and not Private.
Create a Git Personal Access Token (PAT)¶
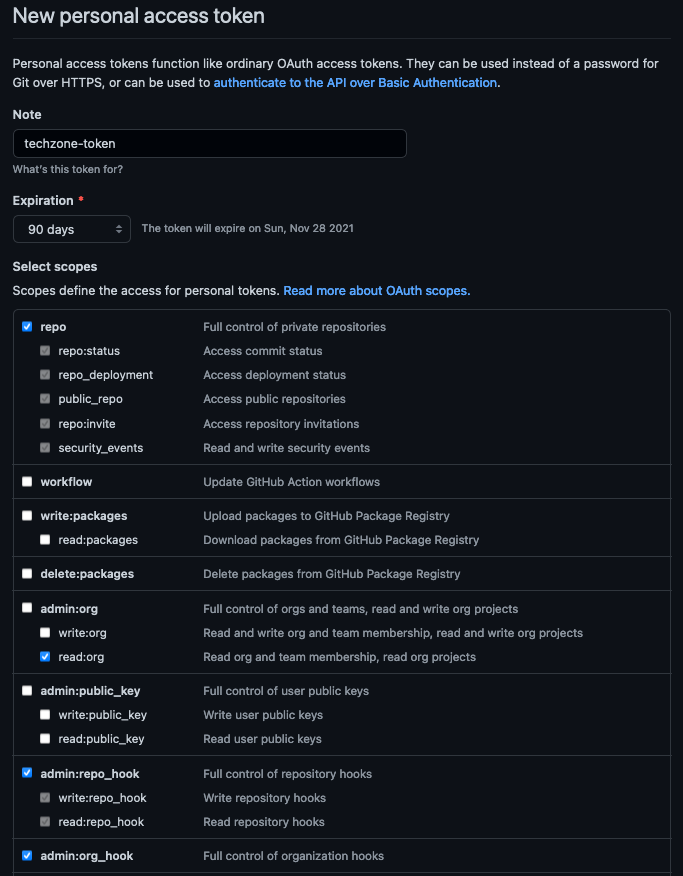
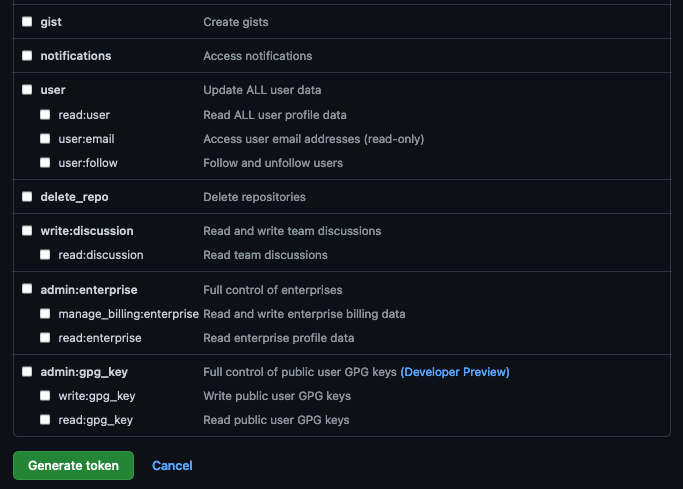
Create a new Git Personal Access Token with the appropriate scopes. This will be required to run the application pipelines or to set up webhooks.
Instructions:
-
Log in to http://github.com and click on Settings.

-
Select Developer settings and click on Personal access tokens.
-
Provide a name for the token, set the
Expirationto 90 days ,set the following scopes and click Generate token.GitHub Personal Access Token scopes
-
Copy and save the Personal Access Token. You will not be able to retrieve this value again later.
Red Hat OpenShift on IBM Cloud cluster with GitOps Configuration¶
Create the cluster¶
-
Provision a Red Hat OpenShift on IBM Cloud cluster with GitOps Configuration from IBM Technology Zone. Select the
OpenShift + GitOps Configurationtile. -
Click the Reserve now radio button.
-
Provide a name for the cluster, select Practice / Self-Education for the purpose and choose the region to provision the cluster.
-
Once a Preferred Geography has been selected, provide the appropriate Worker Node Count and Worker Node Flavor values based on the requirements for this quickstart listed in the note below. Finally, click Submit.
Note
For this IBM App Connect Enterprise Quickstart we recommend you to request the Red Hat OpenShift on IBM Cloud cluster with GitOps Configuration with the following size:
- Worker Node Count = 3
- Worker Node Flavor = 8 CPU x 32 GB
Use the cluster¶
You will receive an email once the cluster provisioning is complete. The email will contain details on the cluster including the ArgoCD Console URL and admin credentials. This same information can also be found on the My reservations from IBM Technology Zone.
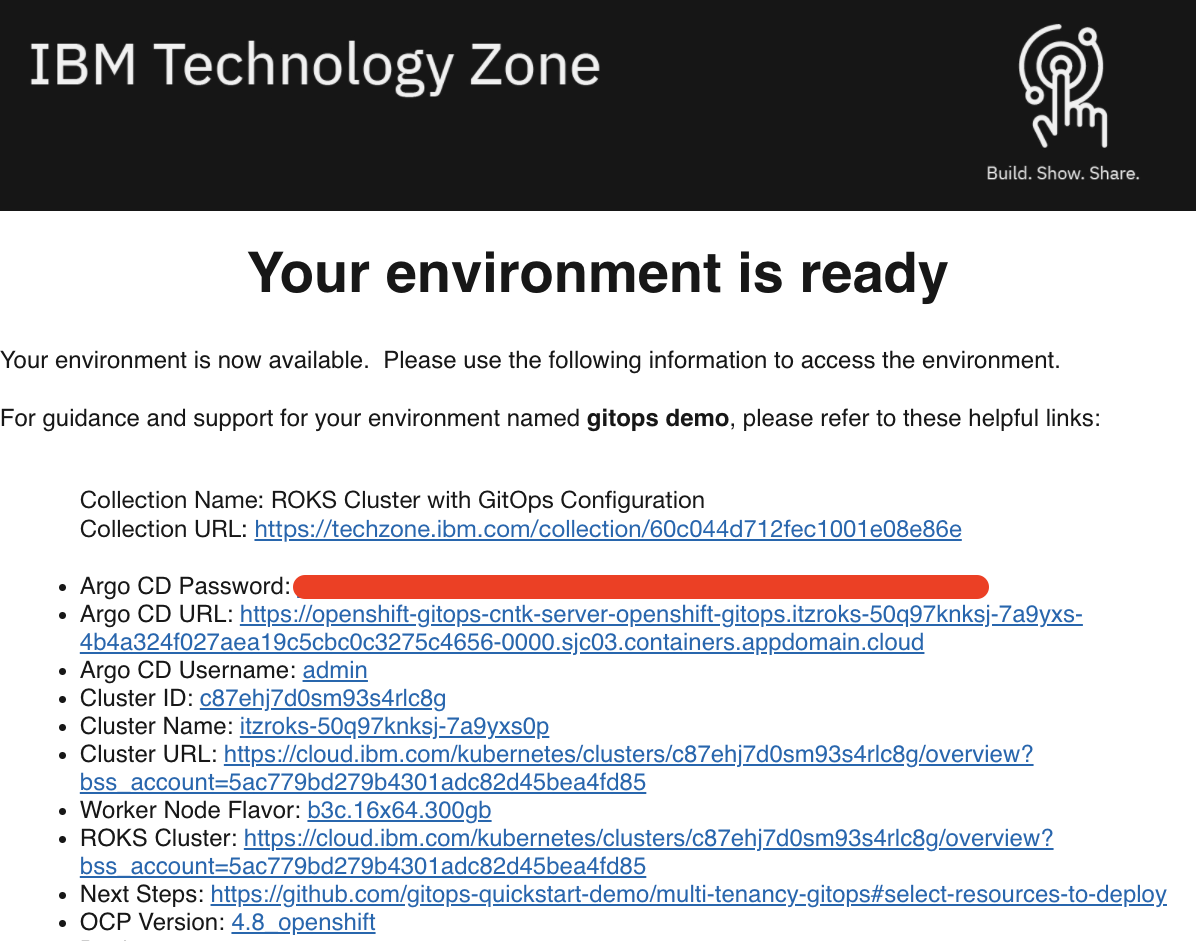
Once your cluster is ready, proceed to the next step to select resources to deploy.
Install required CLIs¶
- Install the Github CLI (version 1.14.0+)
-
Install the OpenShift CLI
oc(version 4.7 or 4.8)-
Log into your OCP cluster, substituting the
--tokenand--serverparameters with your values:oc login --token=<token> --server=<server>If you are unsure of these values, click your user ID in the OpenShift web console and select
Copy login command.
-
-
Install the kubeseal CLI
The kubeseal utility uses asymmetric crypto to encrypt secrets that only the controller can decrypt. These encrypted secrets are encoded in a SealedSecret resource which can safely be checked into your gitops repo. The controller will decrypt the secretes and install into your cluster.
Select resources to deploy¶
- Clone the
multi-tenancy-gitopsrepository in your Git Organization if you have not already done so and select the K8s resources to deploy in the infrastructure and services layers.
Instructions¶
- Select a profile and delete the others from the
0-bootstrapdirectory. If this is your first usage of the gitops workflow, Use thesingle-clusterprofile.GITOPS_PROFILE="0-bootstrap/single-cluster" - Review the
Infrastructurelayer kustomization.yaml and un-comment the resources to deploy to match the IBM App Connect Enterprise recipe . - Review the
Serviceslayer kustomization.yaml and un-comment the resources to deploy to match the IBM App Connect Enterprise recipe . - Commit and push changes to your git repository
git add . git commit -m "initial bootstrap setup" git push origin
Validation¶
- Check the status of the
CommonServiceandPlatformNavigatorcustom resource.# Verify the Common Services instance has been deployed successfully oc get commonservice common-service -n ibm-common-services -o=jsonpath='{.status.phase}' # Expected output = Succeeded # [Optional] If selected, verify the Platform Navigator instance has been deployed successfully oc get platformnavigator -n tools -o=jsonpath='{ .items[*].status.conditions[].status }' # Expected output = True - Log in to the Platform Navigator console
# Retrieve Platform Navigator Console URL oc get route -n tools integration-navigator-pn -o template --template='https://{{.spec.host}}' # Retrieve admin password oc extract -n ibm-common-services secrets/platform-auth-idp-credentials --keys=admin_username,admin_password --to=-